
Industrial SMEs are stepping up the pace with the Internet of Things and Industry 4.0 – which is basically only right and proper. But in one area there is still a problem with implementation.

Top marks for technological commitment – but safety culture trails behind.
By linking the physical and virtual worlds, the digital transformation of the economy represents a historic turning point for industry. Processes, production, products and services are changing radically.
IT security in Industry 4.0.
With the aid of technological innovations and an expanded understanding of automated production processes, industry is becoming more flexible and innovative than ever before: production resources are being networked, processes are being automated and production robots are in tireless action day and night. In the digital factory, rigid production structures are being transformed into modular, efficient systems. This means that formerly “dumb” machines and the products they make are evolving into “smart objects” that communicate with each other and contain within themselves all the proprietary, production and logistics information. The necessary infrastructure for this is the Internet of Things (IoT). This is, so to speak, the grey eminence in the background, without which nothing can happen, networking is impossible and Industry 4.0 is a non-starter.

Many cyber-attacks are only successful because the victims lack security awareness. This is particularly evident in the IoT sector. Udo Schneider, “security evangelist” at Trend Micro, Japanese security company
According to a recent study by Deutsche Telekom, industrial SMEs are well on their way to expanding these technologies. “90 per cent of companies in the logistics, transport and supply sector are already using the IoT today and are planning further expansion. We currently see the biggest wave of introductions (40 per cent) in industry,” it says. That’s the good news. But 82 per cent of the same small and medium-sized companies see the greatest need for investment in connection with IoT projects in IT security – this is the other side of the coin.
Lack of security.
The Internet of Things ensures faster and more efficient production processes, “but at the same time increases companies’ risk of becoming the victims of online attacks. Accordingly, data protection is becoming increasingly complex, time-consuming and expensive for companies,” says a study by Roland Berger Strategy Consultants. The reason for this is the new value creation networks created by the IoT. When billions of things are networked with each other, their vulnerability automatically increases. “Coping with hacker attacks is highly problematic because different areas of a company’s value chain are often affected at the same time,” Roland Berger partner Manfred Hader explains. “Classic IT security areas, however, usually only have business IT in mind, such as communication systems or business applications. Companies should therefore adopt a holistic approach to the problems of cyber security,” says the consultant.
If they don’t, the effects can be dramatic, says expert Prof. Dr Claudia Eckert from the Technical University of Munich. The consequence is that “harmful codes, for example, can be infiltrated into industrial production lines. Even a minimal 0.5 millimetre divergence of a setting a can seriously affect an entire production system and its processes. Or you change the timing, a system suddenly overheats and a robot suddenly does things it shouldn’t. Such attacks pose a huge risk. This is why the issue of the trustworthy digital identity of components, sensors and services is also of great importance in Industry 4.0,” says the expert.
High-security networking.
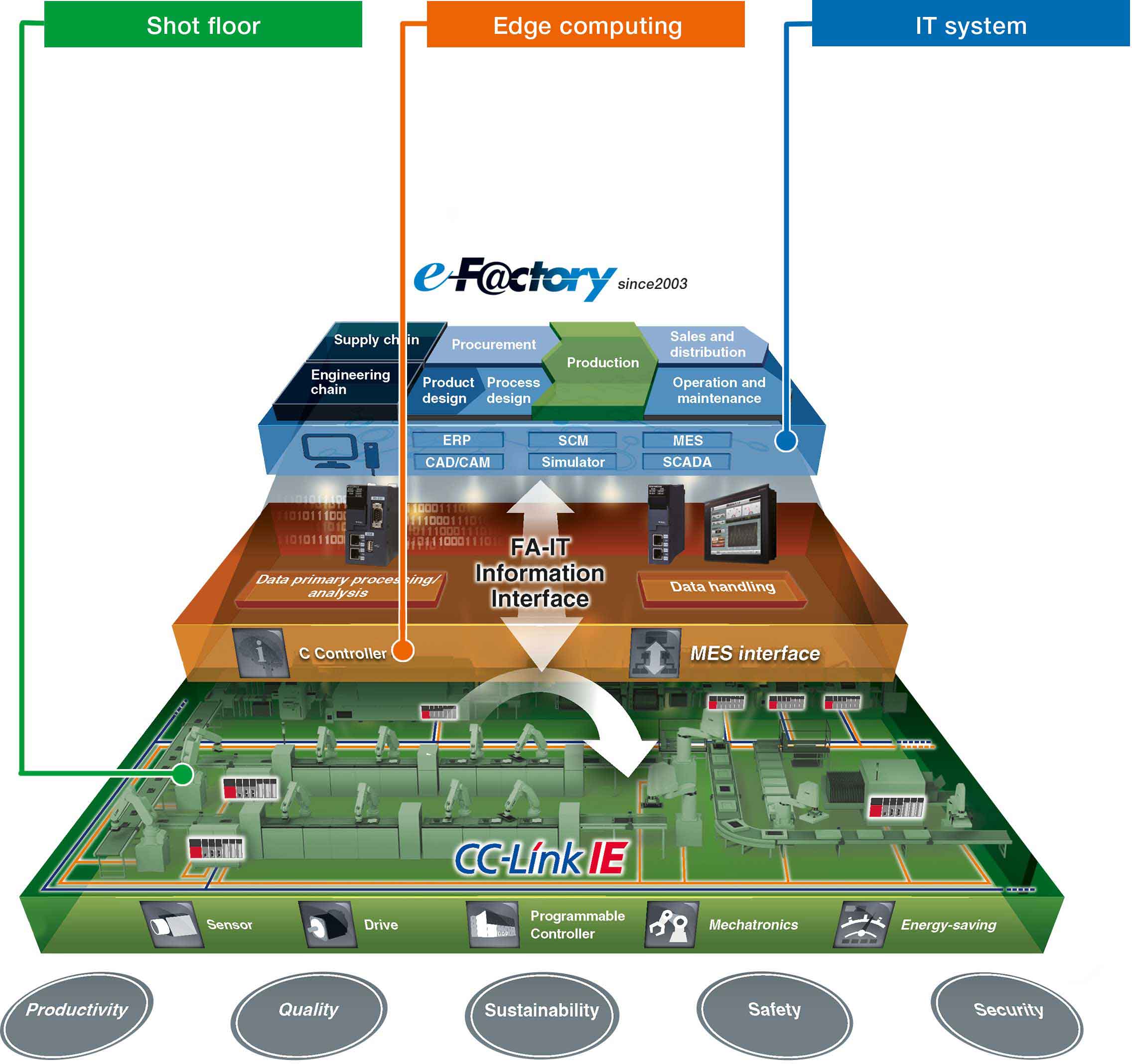
Mitsubishi Electric’s e-F@ctory approach is a smart way of developing cyber-safe, open edge computing solutions for directly connecting production to the cloud.
The first outcome is that the commitment to the IoT in Germany’s industrial SMEs is excellent, but the necessary security is poor or insufficient. So what should be done? As the first and most important step, the specialists of the digital association Bitkom therefore recommend that IT security should be accorded top priority in the company. Next, companies should appoint their own business protection officers or information security officers, who will then address the issue on a broad front. Accordingly, companies must take preventive action and establish a robust IT security management system, keep it up to date at all times, and operate it proactively. This necessitates organisational as well as technical and personnel security during operation.
Udo Schneider, “security evangelist” at Trend Micro, echoes these sentiments. The Japanese security company recently published new study findings on security in the Internet of Things. To this end, 1150 IT and security managers in several countries were surveyed, revealing that many companies have “alarmingly low maturity” with regard to the cyber security of IoT projects. “Many cyber-attacks are only successful because the victims lack security awareness. This is particularly evident in the IoT sector,” says Schneider. It is therefore more of a question of corporate culture than a technical challenge. This is why IoT security must be universally practised, from the boss down to the lowest company level. For example, according to the Trend Micro study, 86 per cent of the IT and security decision-makers surveyed say that IoT threats are not taken seriously enough in their companies. German study participants are particularly critical: 91 per cent of them say that security awareness could be improved, while 47 per cent complain that security is often neglected in IoT projects. This lack of security knowledge, combined with increasing threats and challenges in safeguarding networked devices, “poses a major risk to businesses,” the Tokyo-based company says. According to the study, the focus of cyber-attacks is primarily on networked office equipment (in 59 per cent of cases), followed by production facilities and systems in the supply chain.
One thing is clear: there are now enough mature technological solutions for IoT security. Mitsubishi Electric’s e-F@ctory approach is a smart way of developing cyber-safe, open edge computing solutions for directly connecting production to the cloud. Because only in the cloud will it be possible in the future to comfortably process the gigantic amounts of data that will also be accumulating in medium-sized manufacturing companies from now on. This strategy initially focuses on neatly collecting large amounts of production data, both from the company’s own components and from devices from other suppliers. The freely scalable edge computing solution – with the C-Controller from Mitsubishi Electric as the smallest unit – then processes the data within an automation platform so quickly that delays in the cloud are avoided and real-time production requirements are met. The C-Controller solution transfers the data directly to ERP/MES systems, other cloud solutions or to the company’s own applications. The exchange of the data structure is underpinned by security mechanisms and meets the requirements of IT protection through authentication, identification and up-to-date encryption. The result is the desired networking of value creation, while ensuring a high level of security.
It can be said that it is only proper and important that SMEs are committed to the IoT. However, it would be better to show this commitment in the field of IoT security as well. Technically this is possible, and the only thing that remains to be done is to anchor appropriate awareness of this in the minds of the people involved.
49 % of German companies have incurred some form of loss in recent years as a result of cyber-attacks – large companies with 500 or more employees have been affected slightly more frequently at 58 per cent than small and medium-sized enterprises (SMEs) at 40 per cent.
(Source: Arlington Research on behalf of Kaspersky Lab, March 2019)
74 % of German chemical and pharmaceutical companies have been victims of sabotage, data theft or industrial espionage in the past two years, and another 22 per cent have probably been affected. This is the result of a study by the digital association Bitkom, for which 503 senior managers and security officers from all branches of industry were interviewed. At 68 per cent, companies in the automotive industry are the second most frequent targets – of anything from hacking to file theft. However, machine and plant manufacturers (67 per cent) as well as manufacturers of communications and electrical equipment (63 per cent) were also exposed to a large number of attacks in 2016 and 2017.
(Source: Bitkom, November 2018)
65 % of production environments run on outdated operating systems. “Previously isolated production networks are linked up to the IT network in order to increase efficiency. However, this makes insecure proprietary protocols and potentially decades-old OT devices, which are not patched often enough from the outside due to their great importance for operations, vulnerable to attacks from the outside.”
(Source: Trend Micro, “Securing Smart Factories: Threats to Manufacturing Environments in the Era of Industry 4.0”, April 2019).
31 % of German companies have only one full-time position planned for employees mainly concerned with data protection. Six out of ten companies (59 per cent) have less than one full-time position available for this purpose.
(Source: Bitkom, January 2019)
Fields marked with a * are mandatory.
Mitsubishi Electric Europe B.V.
German Branch
Mitsubishi-Electric-Platz 1
D - 40882 Ratingen
Sales
Tel.: +49 (0)2102 / 486 - 6120
edm.sales@meg.mee.com
Service
Tel.: +49 (0)2102 / 486 - 7600
edm.hotline@meg.mee.com
Applications
Tel.: +49 (0)2102 / 486 - 7700
edm.applikation@meg.mee.com
Spareparts
Tel.: +49 (0)2102 / 486 - 7500
edm.parts@meg.mee.com